OAuth 2.0 Client Types
Jakob Jenkov |
The OAuth 2.0 client role is subdivided into a set of client types and profiles. This text will explain these types and profiles.
The OAuth 2.0 specification defines two types of clients:
- Confidential
- Public
A confidential client is an application that is capable of keeping a client password confidential to the world. This client password is assigned to the client app by the authorization server. This password is used to identify the client to the authorization server, to avoid fraud. An example of a confidential client could be a web app, where no one but the administrator can get access to the server, and see the client password.
A public client is an application that is not capable of keeping a client password confidential. For instance, a mobile phone application or a desktop application that has the client password embedded inside it. Such an application could get cracked, and this could reveal the password. The same is true for a JavaScript application running in the users browser. The user could use a JavaScript debugger to look into the application, and see the client password.
Client Profiles
The OAuth 2.0 specification also mentions a set of client profiles. These profiles are concrete types of applications, that can be either confidential or public. The profiles are:
- Web Application
- User Agent
- Native
Web Application
A web application is an application running on a web server. In reality, a web application typically consists of both a browser part and a server part. If a web application needs access to a resource server (e.g. to Facebook user accounts), then the client password could be stored on the server. The password would thus be confidential.
Here is an illustration of a confidential client web application:
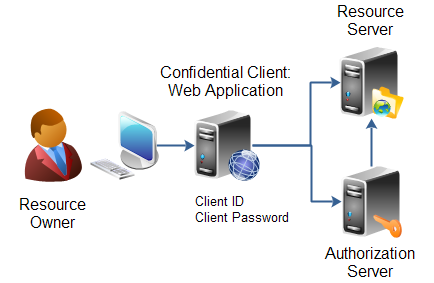 |
| Confidential client: Web Application. |
User Agent Application
A user agent application is for instance a JavaScript application running in a browser. The browser is the user agent. A user agent application may be stored on a web server, but the application is only running in the user agent once downloaded. An example could be a little JavaScript game that only runs in the browser.
Here is an illustration of a client user agent application:
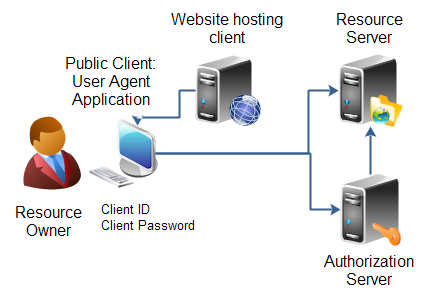 |
| Public client: User Agent Application. |
Native Application
A native application is for instance a desktop application or a mobile phone application. Native applications are typically installed on the users computer or device (phone, tablet etc.). Thus, the client password will be stored on the users computer or device too.
Here is an illustration of a client native application:
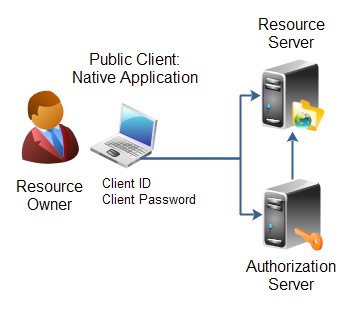 |
| Public client: Native Application. |
Hybrid Applications
Some applications are hybrids of these profiles. For instance, a native application can have a server part too, that does part of the work (e.g. store data). The OAuth 2.0 specification says nothing about such hybrids. However, in most cases a hybrid will be able to use the authentication models of one of these profiles.
| Tweet | |
Jakob Jenkov | |











